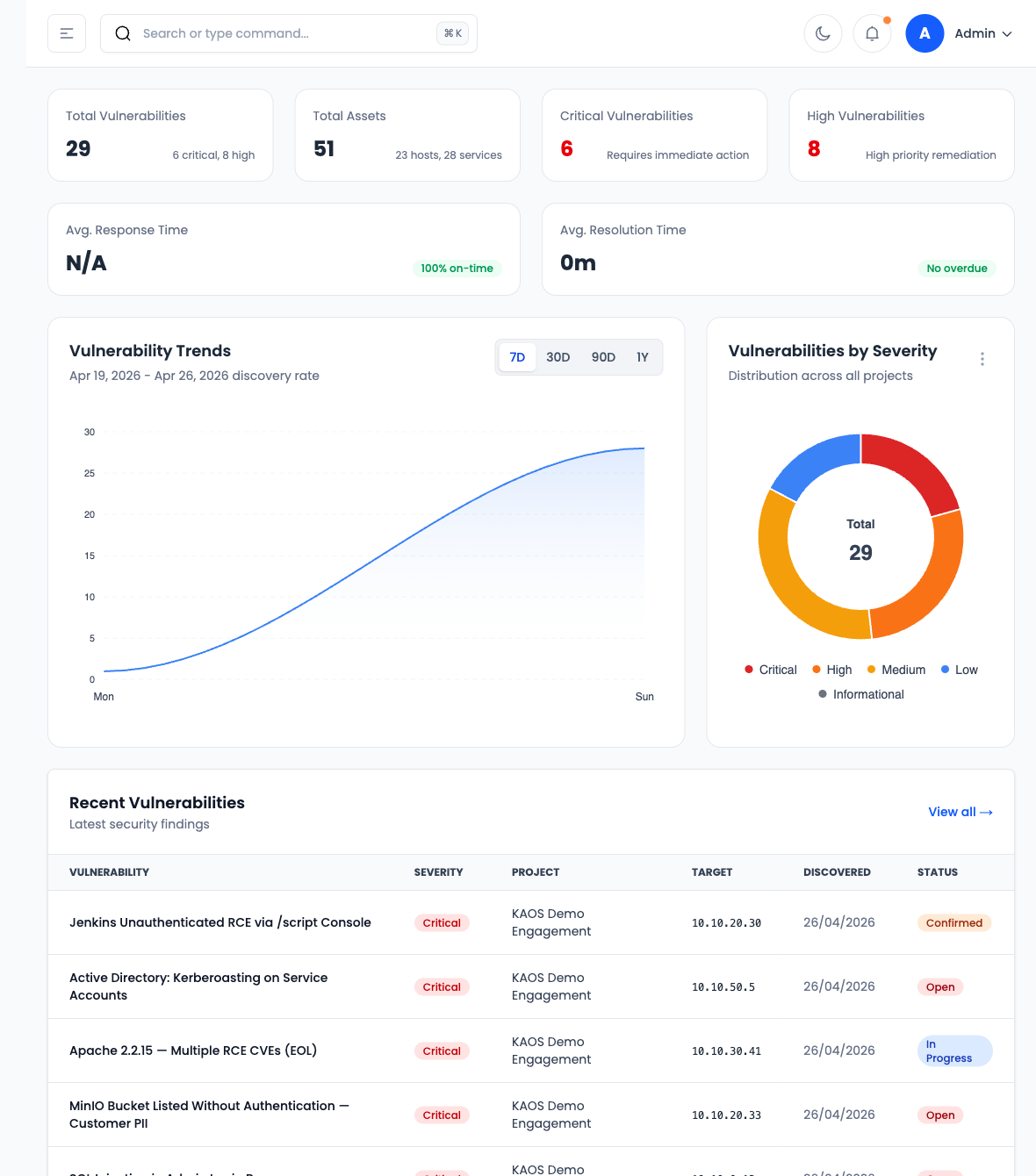
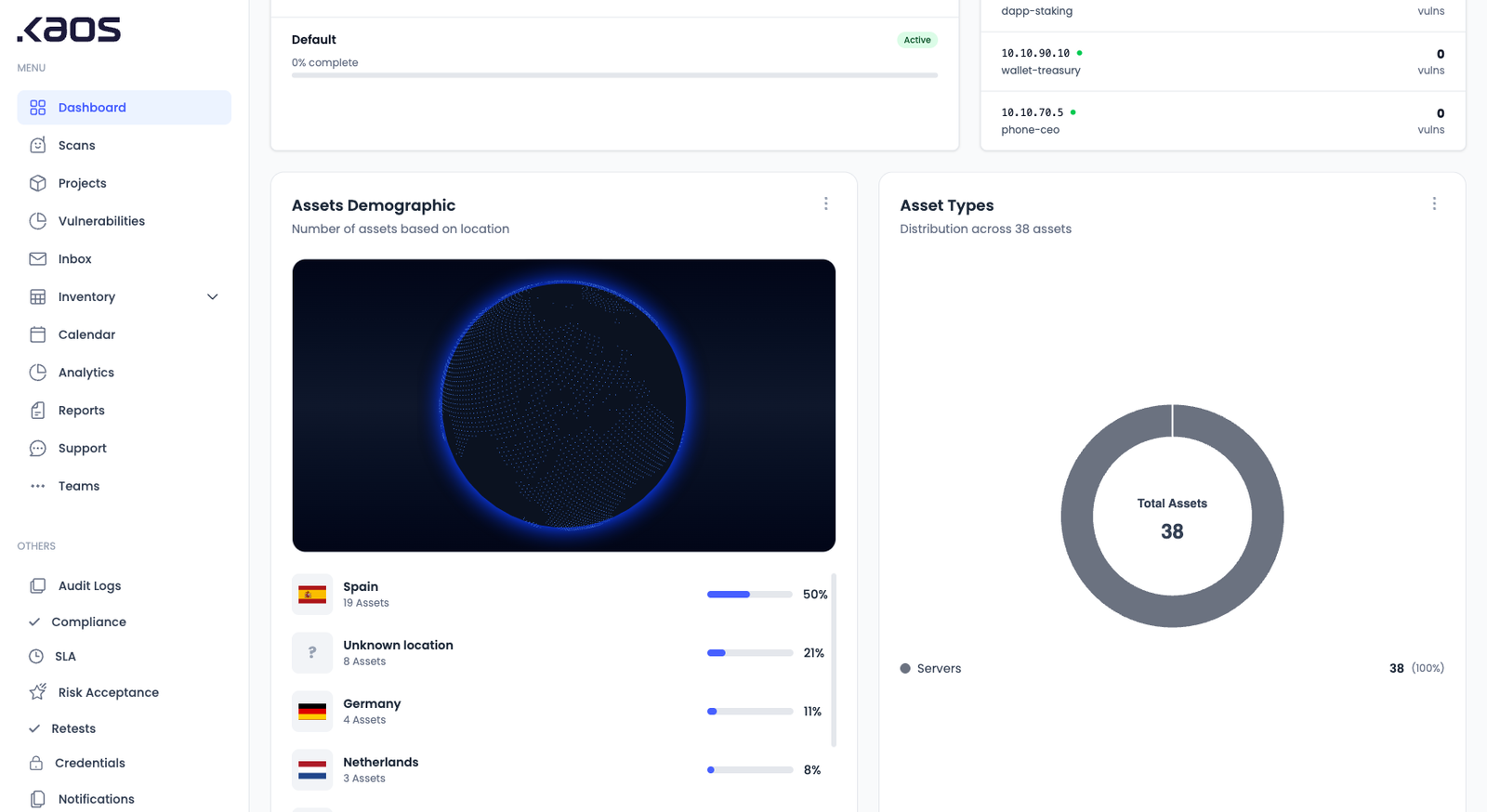
KAI runs the pentest. Then proves it.
Recon, exploitation, attack-chain analysis, and a reproducible PoC for every finding — written by an agent trained on OSCP, OSCE3, and CRTO methodology.
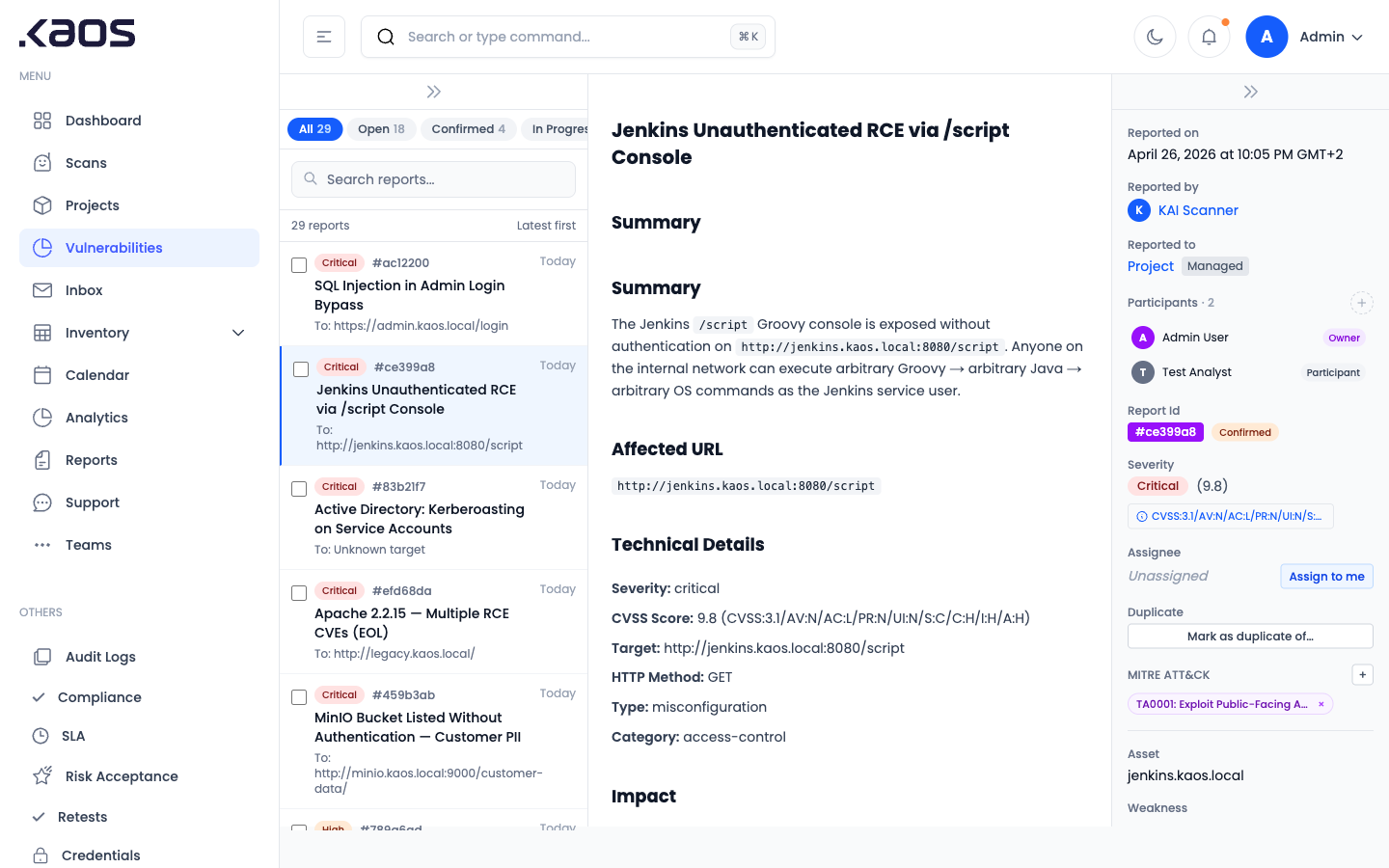
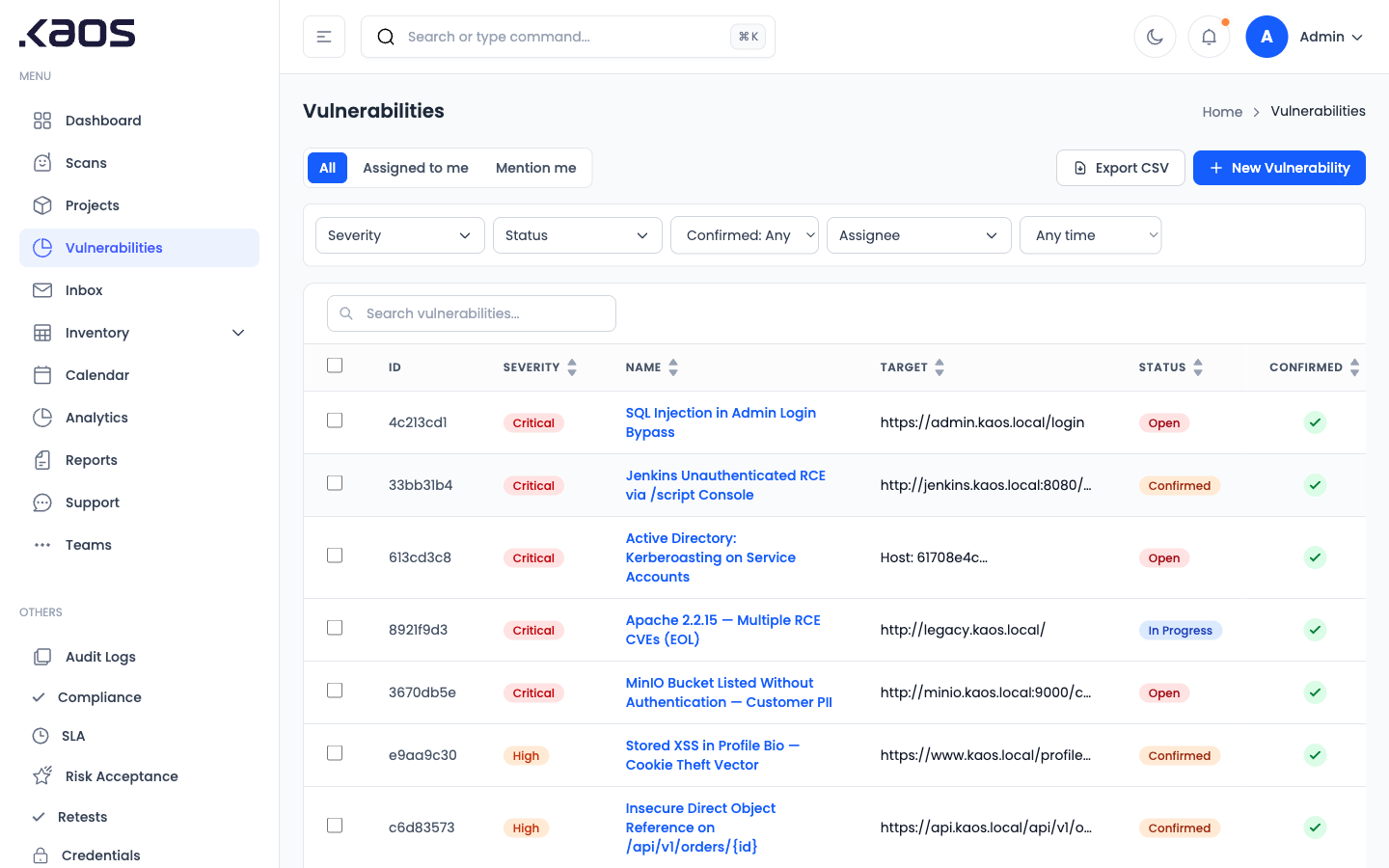
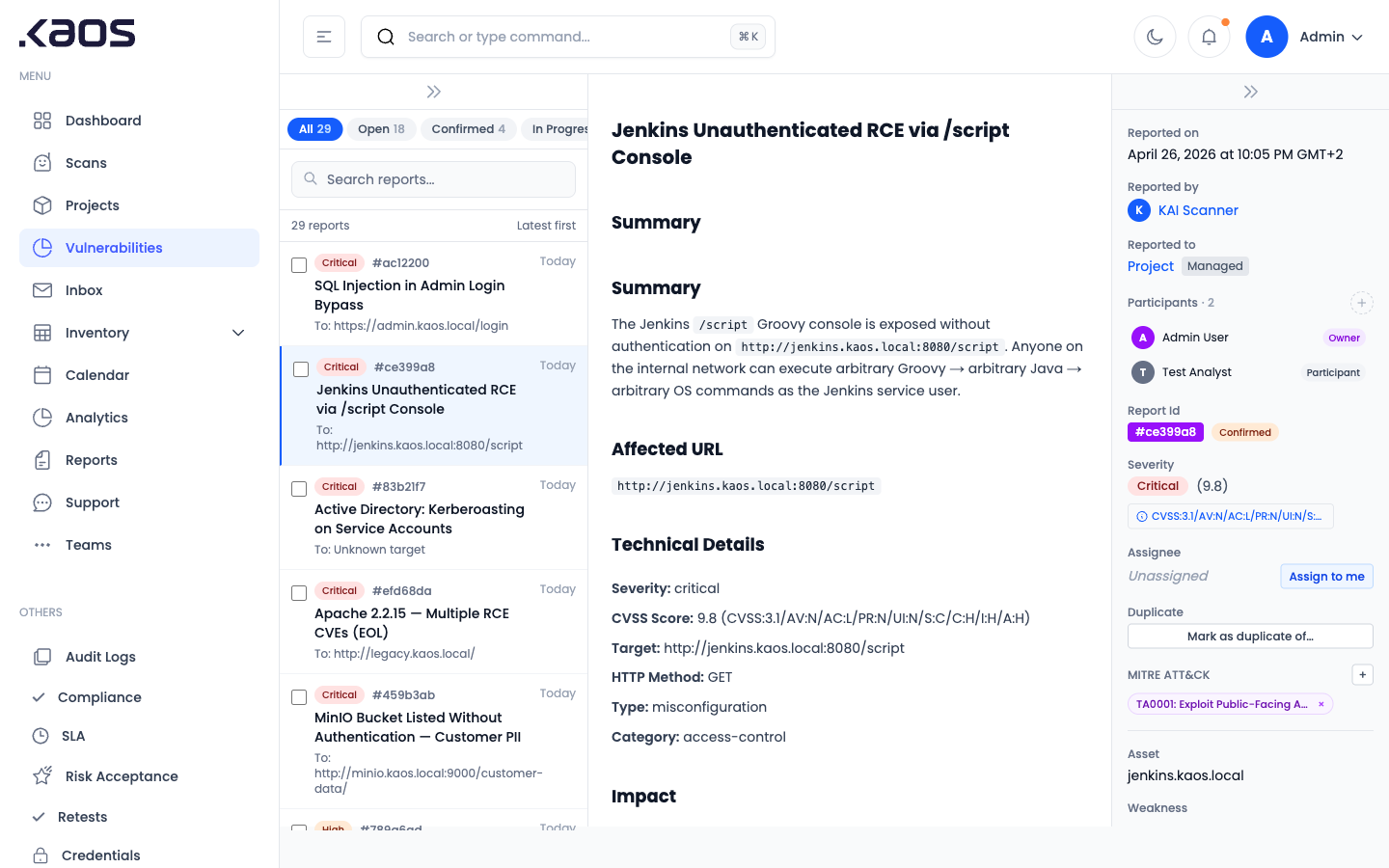
Every vulnerability KAI reports is validated with a reproducible proof of concept — built by an agent designed and trained by certified offensive security practitioners.
Validated, Not Theoretical
Every finding ships with a working proof of exploitation. No more 400-page reports of unverified CVE matches.
Thinks Like an Attacker
KAI chains weaknesses into full attack paths the way an OSCP-grade pentester would — not a checklist scanner.
Continuous, Not Quarterly
Trigger autonomous assessments on every release, every asset change, or on a schedule. CI/CD ready.